Checkov is a static code analysis tool for infrastructure-as-code.
It scans cloud infrastructure provisioned using Terraform, Terraform plan, Cloudformation, Kubernetes, Serverless or ARM Templates and detects security and compliance misconfigurations.
Checkov also powers Bridgecrew, the developer-first platform that codifies and streamlines cloud security throughout the development lifecycle. Bridgecrew identifies, fixes, and prevents misconfigurations in cloud resources and infrastructure-as-code files.


- Over 500 built-in policies cover security and compliance best practices for AWS, Azure and Google Cloud.
- Scans Terraform, Terraform Plan, CloudFormation, Kubernetes, Serverless framework and ARM template files.
- Detects AWS credentials in EC2 Userdata, Lambda environment variables and Terraform providers.
- Evaluates Terraform Provider settings to regulate the creation, management, and updates of IaaS, PaaS or SaaS managed through Terraform.
- Policies support evaluation of variables to their optional default value.
- Supports in-line suppression of accepted risks or false-positives to reduce recurring scan failures. Also supports global skip from using CLI.
- Output currently available as CLI, JSON, JUnit XML and github markdown and link to remediation guides.
Scan results in CLI
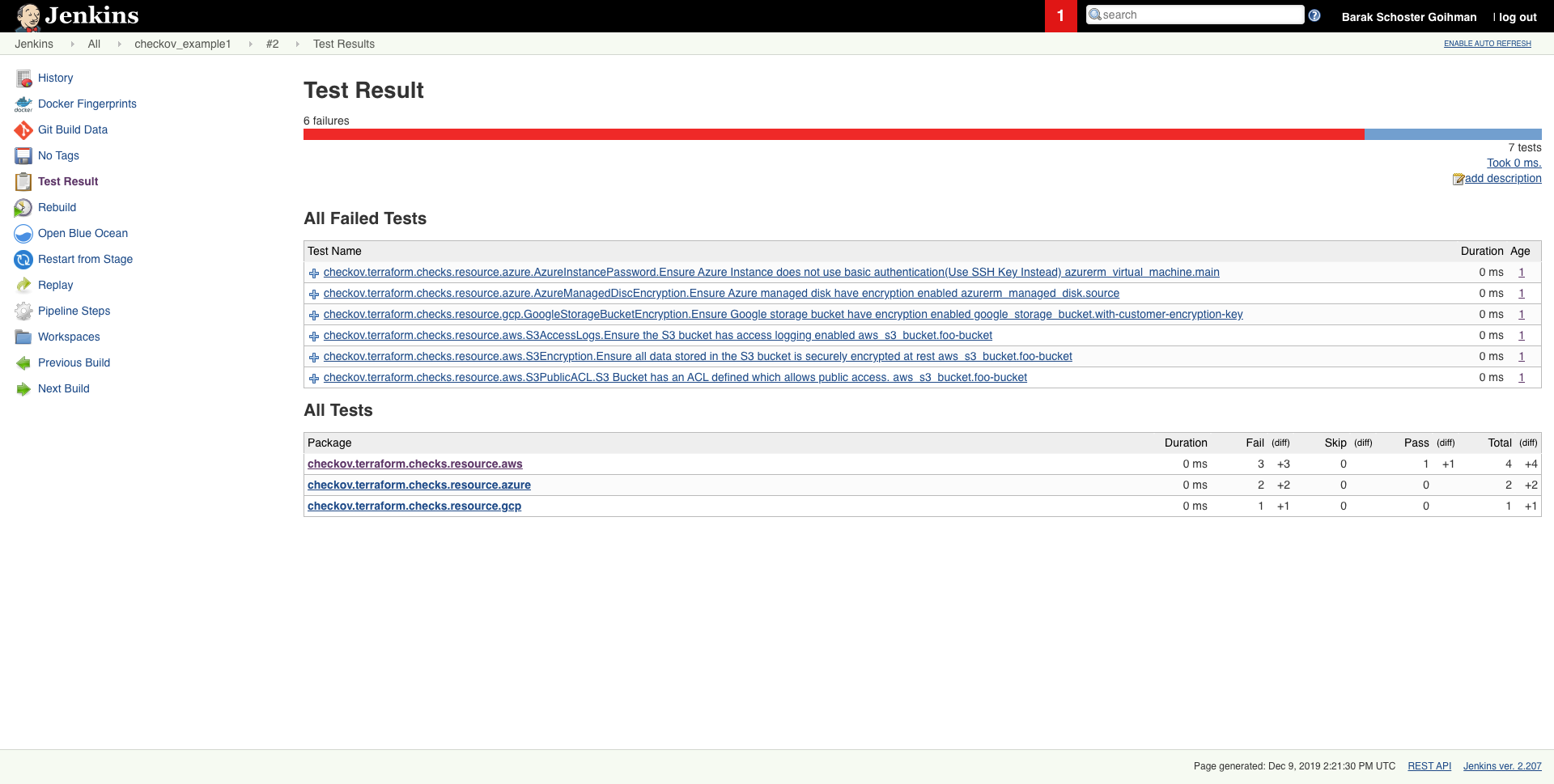
Scheduled scan result in Jenkins
- Python >= 3.7 (Data classes are available for Python 3.7+)
- Terraform >= 0.12
pip3 install checkovInstallation on Alpine:
pip3 install --upgrade pip && pip3 install --upgrade setuptools
pip3 install checkovInstallation on Ubuntu 18.04 LTS:
Ubuntu 18.04 ships with Python 3.6. Install python 3.7 (from ppa repository)
sudo apt update
sudo apt install software-properties-common
sudo add-apt-repository ppa:deadsnakes/ppa
sudo apt install python3.7
sudo apt install python3-pip
sudo python3.7 -m pip install -U checkov #to install or upgrade checkov)or using homebrew (MacOS only)
brew install checkovor
brew upgrade checkovif you installed checkov with pip3
pip3 install -U checkovcheckov --directory /user/path/to/iac/codeOr a specific file or files
checkov --file /user/tf/example.tfOr
checkov -f /user/cloudformation/example1.yml -f /user/cloudformation/example2.ymlOr a terraform plan file in json format
terraform init
terraform plan -out tf.plan
terraform show -json tf.plan > tf.json
checkov -f tf.jsonNote: terraform show output file tf.json will be single line.
For that reason all findings will be reported line number 0 by checkov
check: CKV_AWS_21: "Ensure all data stored in the S3 bucket have versioning enabled"
FAILED for resource: aws_s3_bucket.customer
File: /tf/tf.json:0-0
Guide: https://docs.bridgecrew.io/docs/s3_16-enable-versioningIf you have installed jq you can convert json file into multiple lines with the following command:
terraform show -json tf.plan | jq '.' > tf.json Scan result would be much user friendly.
checkov -f tf.json
Check: CKV_AWS_21: "Ensure all data stored in the S3 bucket have versioning enabled"
FAILED for resource: aws_s3_bucket.customer
File: /tf/tf1.json:224-268
Guide: https://docs.bridgecrew.io/docs/s3_16-enable-versioning
225 | "values": {
226 | "acceleration_status": "",
227 | "acl": "private",
228 | "arn": "arn:aws:s3:::mybucket",
Passed Checks: 1, Failed Checks: 1, Suppressed Checks: 0
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/main.tf:
Passed for resource: aws_s3_bucket.template_bucket
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/../regionStack/main.tf:
Failed for resource: aws_s3_bucket.sls_deployment_bucket_name Start using Checkov by reading the Getting Started page.
docker pull bridgecrew/checkov
docker run --tty --volume /user/tf:/tf bridgecrew/checkov --directory /tfNote: if you are using Python 3.6(Default version in Ubuntu 18.04) checkov will not work and it will fail with ModuleNotFoundError: No module named 'dataclasses' error message. In this case, you can use the docker version instead.
Note that there are certain cases where redirecting docker run --tty output to a file - for example, if you want to save the Checkov JUnit output to a file - will cause extra control characters to be printed. This can break file parsing. If you encounter this, remove the --tty flag.
Using command line flags you can specify to run only named checks (allow list) or run all checks except those listed (deny list).
List available checks:
checkov --list Allow only 2 checks to run:
checkov --directory . --check CKV_AWS_20,CKV_AWS_57Run all checks except 1 specified:
checkov -d . --skip-check CKV_AWS_52Run all checks except checks with specified patterns:
checkov -d . --skip-check CKV_AWS*For Kubernetes workloads, you can also use allow/deny namespaces. For example, do not report any results for the kube-system namespace:
checkov -d . --skip-check kube-systemLike any static-analysis tool it is limited by its analysis scope. For example, if a resource is managed manually, or using subsequent configuration management tooling, a suppression can be inserted as a simple code annotation.
To skip a check on a given Terraform definition block or CloudFormation resource, apply the following comment pattern inside it's scope:
checkov:skip=<check_id>:<suppression_comment>
<check_id>is one of the available check scanners<suppression_comment>is an optional suppression reason to be included in the output
The following comment skip the CKV_AWS_20 check on the resource identified by foo-bucket, where the scan checks if an AWS S3 bucket is private.
In the example, the bucket is configured with a public read access; Adding the suppress comment would skip the appropriate check instead of the check to fail.
resource "aws_s3_bucket" "foo-bucket" {
region = var.region
#checkov:skip=CKV_AWS_20:The bucket is a public static content host
bucket = local.bucket_name
force_destroy = true
acl = "public-read"
}
The output would now contain a SKIPPED check result entry:
...
...
Check: "S3 Bucket has an ACL defined which allows public access."
SKIPPED for resource: aws_s3_bucket.foo-bucket
Suppress comment: The bucket is a public static content host
File: /example_skip_acl.tf:1-25
...To suppress checks in Kubernetes manifests, annotations are used with the following format:
checkov.io/skip#: <check_id>=<suppression_comment>
For example:
apiVersion: v1
kind: Pod
metadata:
name: mypod
annotations:
checkov.io/skip1: CKV_K8S_20=I don't care about Privilege Escalation :-O
checkov.io/skip2: CKV_K8S_14
checkov.io/skip3: CKV_K8S_11=I have not set CPU limits as I want BestEffort QoS
spec:
containers:
...For detailed logging to stdout setup the environment variable LOG_LEVEL to DEBUG.
Default is LOG_LEVEL=WARNING.
To skip a whole directory, use the environment variable CKV_IGNORED_DIRECTORIES.
Default is CKV_IGNORED_DIRECTORIES=node_modules,.terraform,.serverless
If you want to use checkov's within vscode, give a try to the vscode extension availble at vscode
For Terraform compliance scanners check out tfsec and Terraform AWS Secure Baseline for secured basline.
For CloudFormation scanning check out cfripper and cfn_nag.
For Kubernetes scanning check out kube-scan and Polaris.
Contribution is welcomed!
Start by reviewing the contribution guidelines. After that, take a look at a good first issue.
Looking to contribute new checks? Learn how to write a new check (AKA policy) here.
checkov does not save, publish or share with anyone any identifiable customer information.
No identifiable customer information is used to query Bridgecrew's publicly accessible guides.
checkov uses Bridgecrew's API to enrich the results with links to remediation guides.
To skip this API call use the flag --no-guide.
Bridgecrew builds and maintains Checkov to make policy-as-code simple and accessible.
Start with our Documentation for quick tutorials and examples.
If you need direct support you can contact us at [email protected].